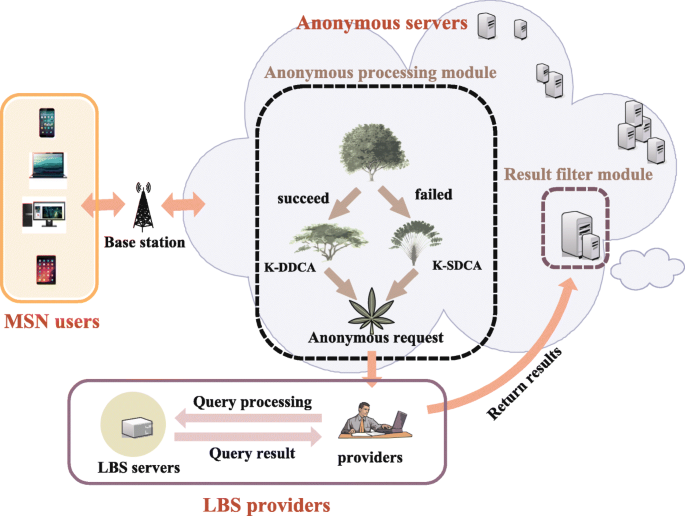
Shows a semi-trusted anonymous server location service framework, which... | Download Scientific Diagram
Anonymous, French, 19th century | Designs for a Decorative Frieze, Two Planters and a Server | The Metropolitan Museum of Art

Anonymous Internet - Grier Forensics | Creating advanced technology to defend our nation through the power of science



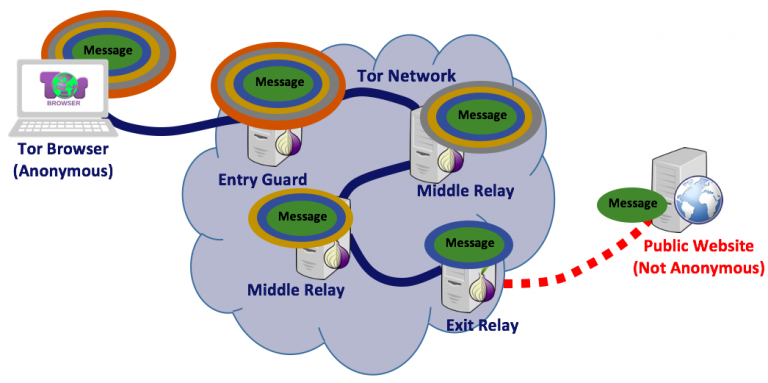
![Host a Deep Web IRC Server for More Anonymous Chatting Online [Tutorial] - YouTube Host a Deep Web IRC Server for More Anonymous Chatting Online [Tutorial] - YouTube](https://i.ytimg.com/vi/67f9iptWqt0/maxresdefault.jpg)